Synapsa Platform
Comprehensive toolbox consisting of four modules focused on a specific issue we see in daily security operations.

Identifying of security breach takes organizations 212 days and another 75 days to actually contain it.
Cybersecurity without automation is a losing game.
We fully understand the fact, companies already have multiple tools which they struggle to manage and maintain. Introducing a new tool into the environment has to be quick and easy.
Synapsa Platform can be deployed literally anywhere and within a few minutes, we are leveraging docker technology to make you install based on your preferences. Typical deployment takes less than 90 minutes of your time, but saves hours of manual work.
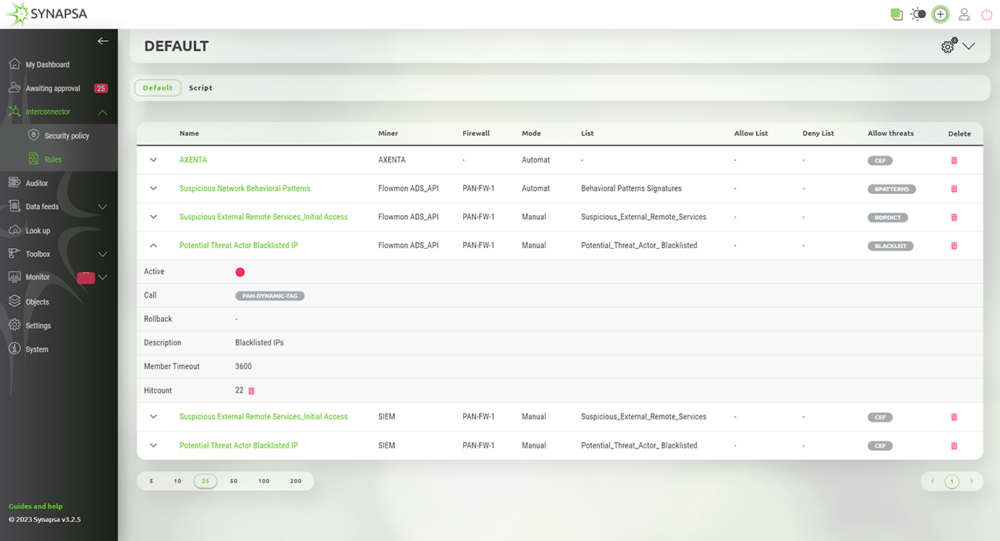
The middleware which automatically processes input data from any source (miner) capable of sending syslog such as SIEM, Firewalls, Proxy, Servers and other endpoints. By leveraging the built-in parsers it is possible to extract any data and reuse it in various automation tasks. Discover more...
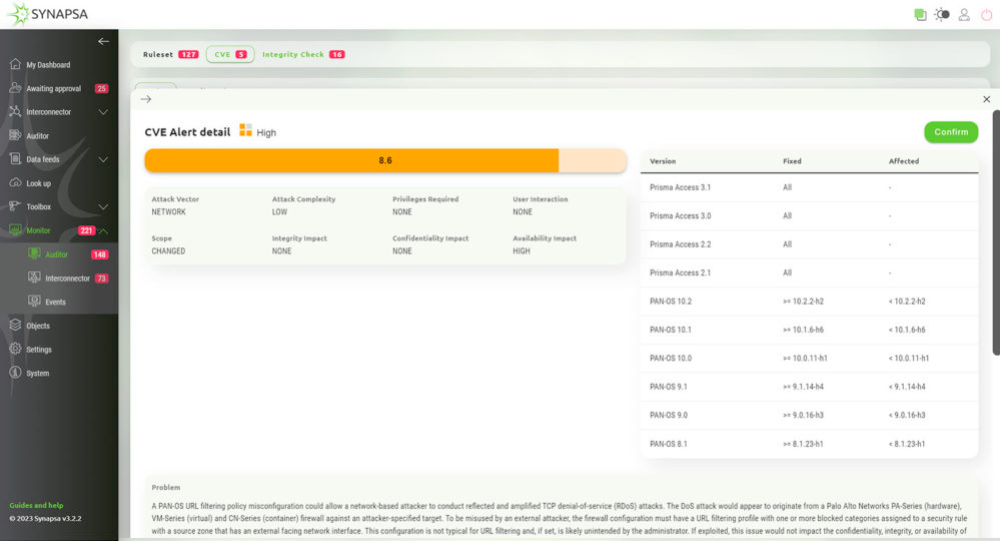
Consists of three parts, which allow operators to have complete control over the configuration and compliance with your standards or any industry benchmark. Discover more...
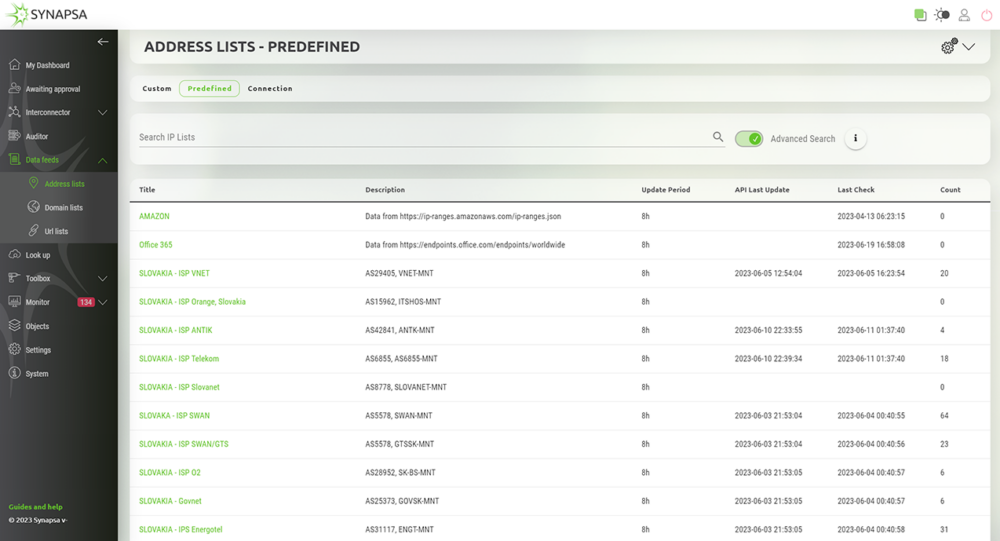
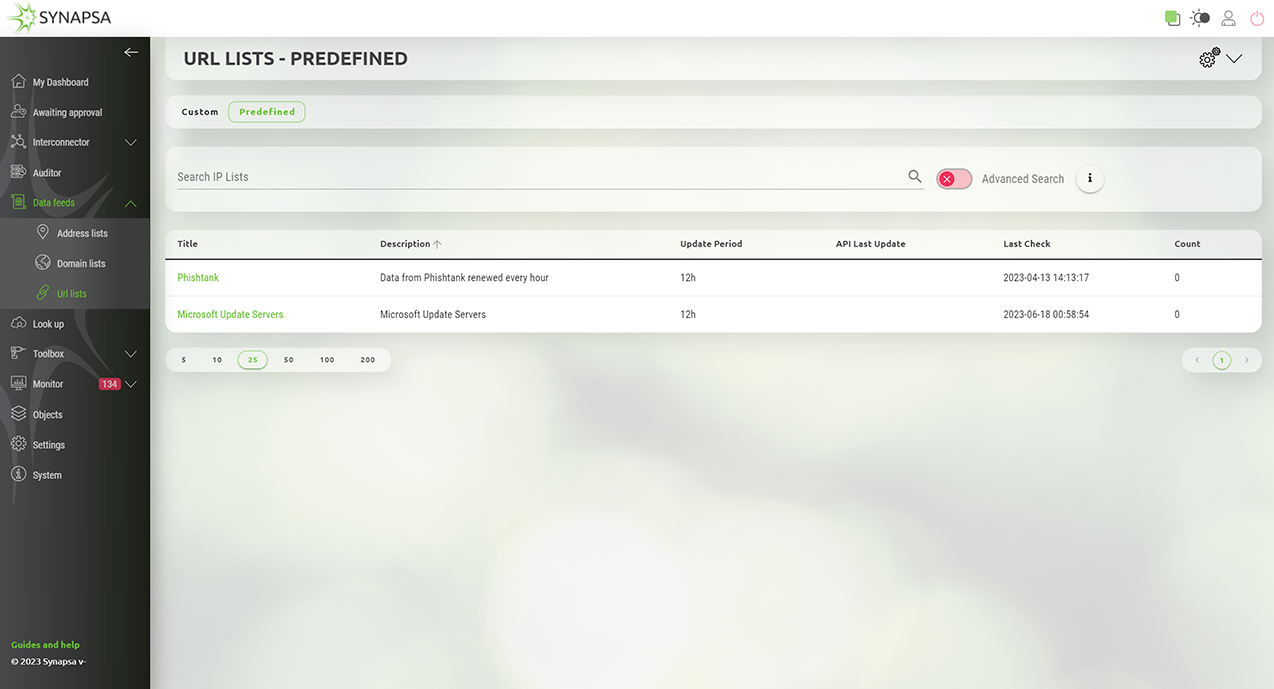
A group of smart dynamic object lists consisting of threat intelligence data to feed your cybersecurity mitigation devices like firewalls, proxy or cloud infrastructure to protect your environment from the latest indicators of compromise (IoCs). Discover more...
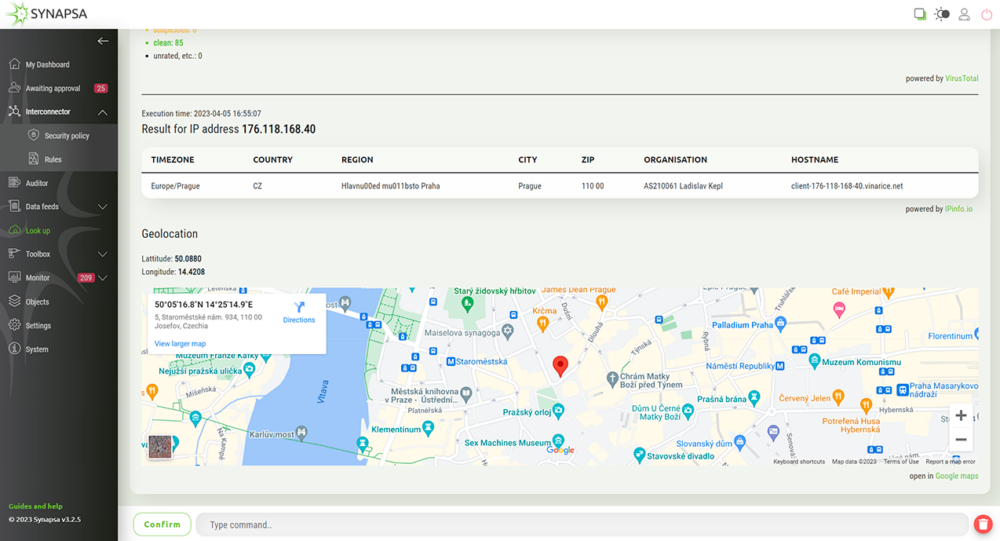
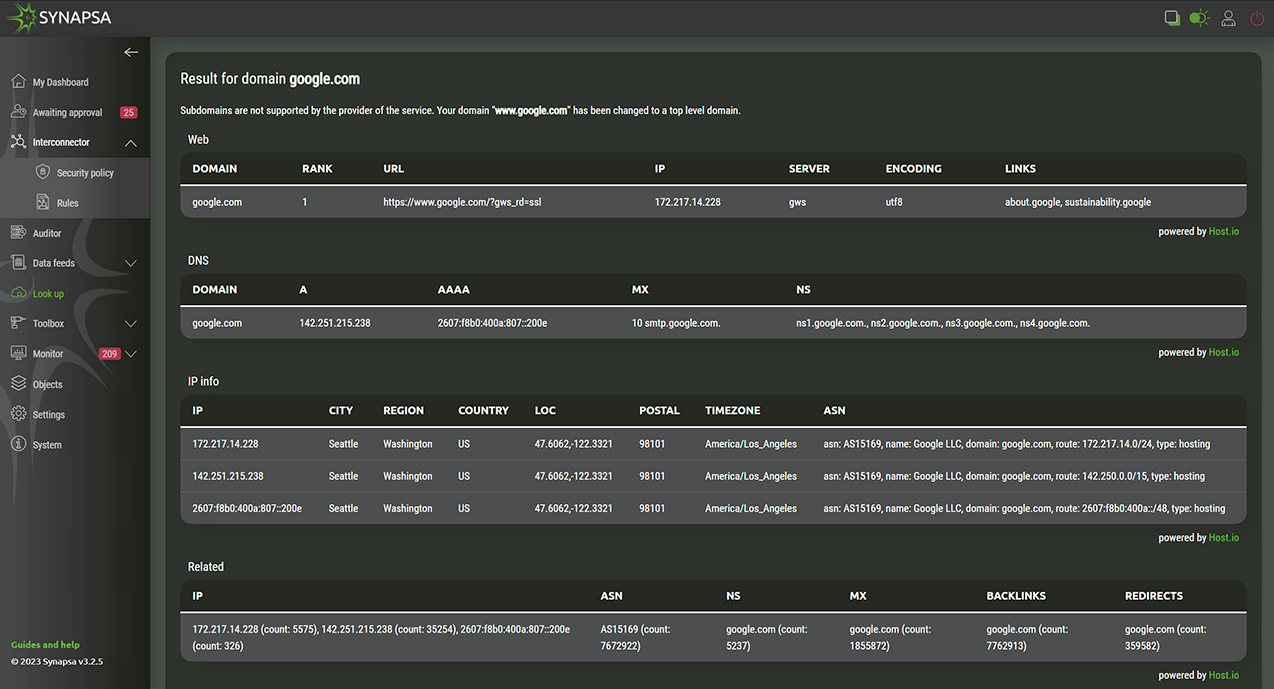
Provides a single pane of glass for data enrichment from any 3rd party API provider, which allows analysts to easily fetch data and use it for event investigation. Discover more...
Real-time compliance monitoring
Synapsa Auditor will make sure your firewall ruleset and configuration has no hidden caveats which could invite attackers into your organization. This check will be happening constantly, every second, to make sure your organization is safe.
CIS Benchmark compliance in minutes
Ensure your devices are configured according to the CIS Benchmark best practices literally in minutes. Synapsa gives you exact cli commands to fix your configuration issues, all effortless and real-time.
Out of the box event parser
Gives you the ability to send any event from any device to Synapsa interconnector, without expecting you to parse and extract the interesting data out of the raw syslog.
Comprehensive API toolbox
Today’s world is all about integration, cooperation and automation. Synapsa gives you ability to interconnect your legacy, syslog exporting devices, to talk to the new API capable gear to take an action you need, not to bother your engineers with task machine can do quicker and automatically.
Out of the box data feeds
The internet is a dangerous place full of malicious URLs, IPs and files. Synapsa collects all the feeds based on your needs, converts them to standardized format, which your firewall understands, to block malicious traffic before breach or even command and control communication happens.
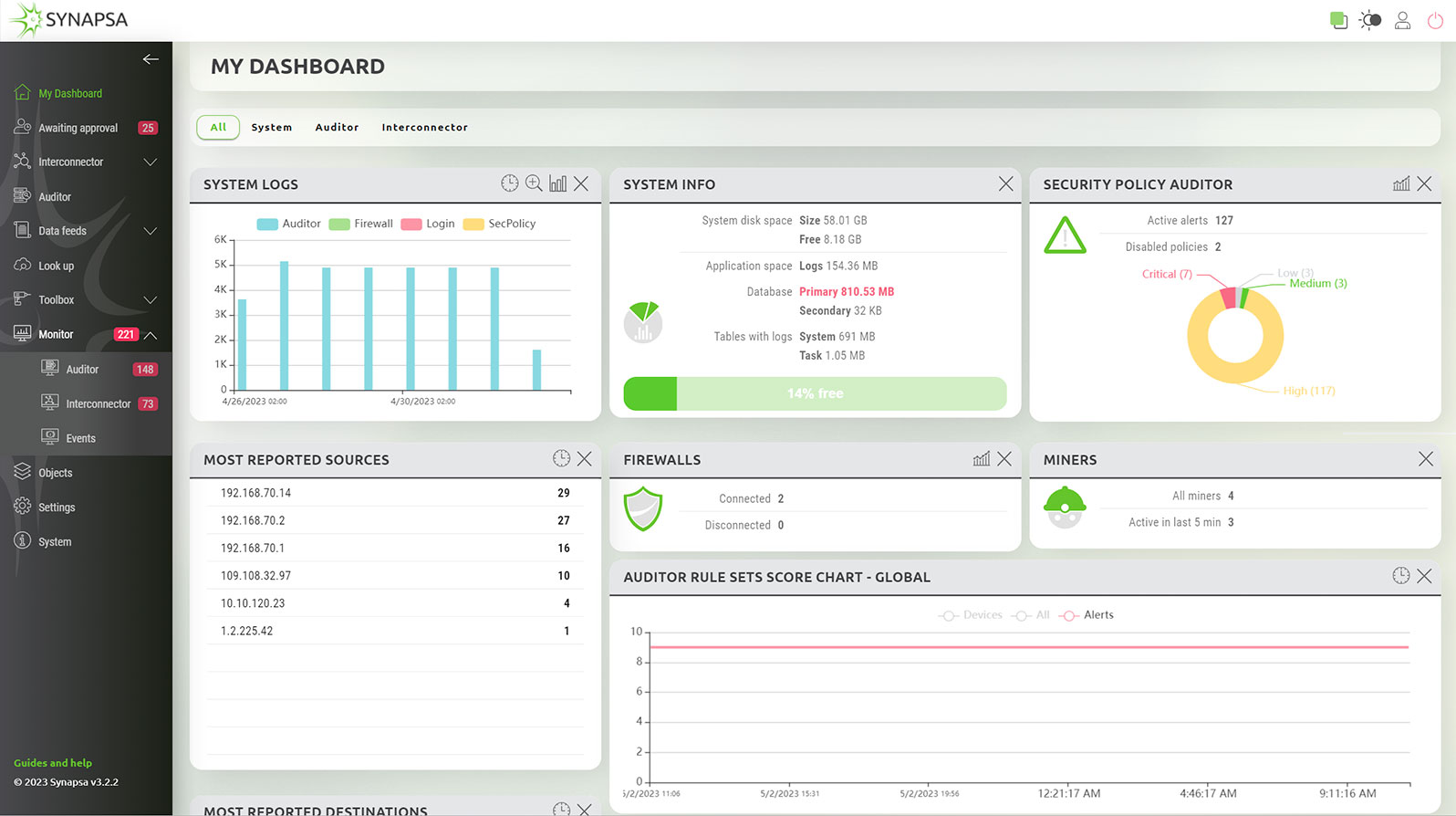
Comprehensive dashboard
Reporting and visualization is the key feature in order to understand your environment and the security gaps your organization is facing. SYNAPSA offers very comprehensive dashboards for every module, including timeline graphs and very unique security index score
© 2026 Synapsa Networks
designed by illusmart
This website use cookies and analytical data. In case you agree with that please click on the "I agree" button bellow. Details can be found on a page Information for the processing of personal data.